Derek Schenk
CTO at Datex Inc
Derek Schenk's Professional Contact Details
Email (Verified)
****@datex.ca
HQ
+1 905-822-2300
Location
Toronto, Ontario, Canada
Company
Datex Inc

Person Seniority
c_suite

Person Functions
information technology
Derek Schenk's Current Company Details
A paradigm-shifting approach to data protection. DataStealth is a revolutionary approach to securing and protecting your most valuable business assets: your data and documents. Instead of trying to...
A paradigm-shifting approach to data protection. DataStealth is a revolutionary approach to securing and protecting your most valuable business assets: your data and documents. Instead of trying to block unauthorized access at the perimeter of an IT environment, DataStealth removes sensitive information from within data and documents BEFORE it enters an IT environment, so that should that environment ever be breached, there would be no sensitive data or documents to steal. DataStealth combines your organization's privacy, regulatory, compliance and other standards and requirements, with DataStealth's suite of tokenization, de-identification and encryption options, to create an easily configurable and flexible data protection policy. Once activated, the policy is applied to all network traffic passing through DataStealth. When any network traffic matches any one of the active data protection policies, DataStealth springs into action and applies your privacy, regulatory, compliance and other standards and requirements to the data and documents as they pass through DataStealth, in real-time. Endpoints that are downstream of DataStealth no longer have any sensitive information. And for that reason, in the event of a network breach, whether it is external or internal in nature, there is no sensitive information to steal. With DataStealth, intruders cannot steal what is not there.

Founded Year
1991

Organization Website
datex.ca

Organization Languages
English

Organization Revenue
2000

Current Technologies
route 53
gmail
google apps
amazon aws
hubspot
mobile friendly
linkedin widget
linkedin login
google analytics
google plus login
secure storage
cloud security
test data management
cloud access service broker
tokenization
data protection
gdpr
dlp
data security
data residency
data deidentification
data masking
information technology & services
information technology
computer & network security
Derek Schenk's Work History and Education
Datex Inc.
CTO
2014 - Present
Colleagues at Datex Inc
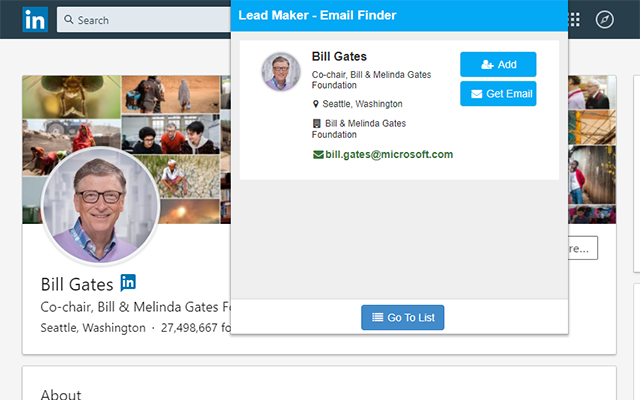
Prospect on LinkedIn
Find emails on Linkedln, Sales Navigator, AngelList, CrunchBase, Google etc.
Download
Extension